According to OWASP, SQL injection is one of the top 10 most commonly found vulnerabilities in web applications. In this tutorial we are going to show you how...
Author - Ajay Verma
A Computer Science Graduate, who works extensively on open source projects. His Areas Of interest are: Network Security, Linux Administration, FOSS, Python, and C programming.
There are often times when you come across programs that eat up your system resources unnecessarily. There can be many reasons why a program is behaving in...
One of the best way to ensure network stability is through iperf testing. For network tuning and assessment iperf is a flexible choice. It estimates the total...
pfSense is one of the most versatile firewall systems available out there in the market. It uses BSD as its base operating system. pfSense is based on...
There are multiple scenarios where you will be required to reset Cisco router password without knowing it. For example if your network administrator left the...
Apache is most widely used web server in the world by market-share right now. It’s amazingly flexible when it comes to handle large amount of traffic...
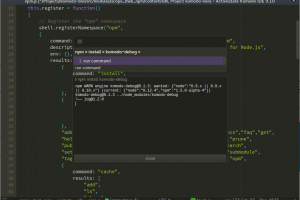
Python online IDE Python online editor gives you the ability to run and debug your code online without setting up the python development environment. Python is...
Today we are going to look at some of the best free cloud storage services and file sharing services. Most of these best free cloud storage services allow file...
What is Vulnerability assessment? When Securing organization’s assets, knowledge is power. In today’s world as businesses grow, their dependency on...
What is penetration testing? In this article we are going to breakdown the basics of penetration testing. People who are new to information security and want...